In brief⚡
**The exploit medium of Euler Finance is Flash Loans & Logical Vulnerability.
Poolz Finance on Ethereum lost ~$500K due to a contract vulnerability.
A flash loan attack on Euler Finance led to a loss of ~$197M.
Yearn Finance lost ~$1.38M due to the Euler Hack.
Idle Finance lost ~$10.99M due to the Euler Hack.
Yield Protocol lost ~$1.5M due to the Euler Hack.
Hedera lost ~$515K due to a vulnerable smart contract
Hacks and Scams⚠️
Poolz Finance
Amount of Loss: ~ $555K
Analysis
Poolz Finance's LockedDeal contract was hacked, resulting in a loss of approximately $555,000.
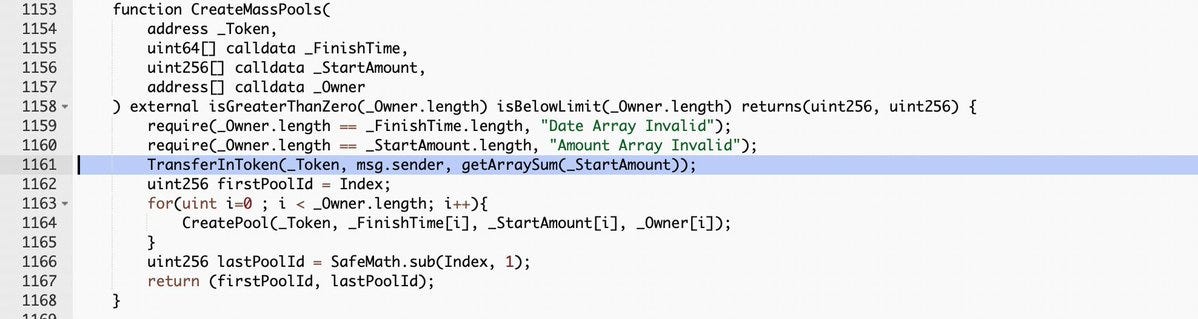
The attacker used the LockedDeal contract's vulnerable function CreateMassPools to trigger an integer overflow vulnerability in the parameter
_StartAmount.The attacker obtained other tokens in addition to a large number of poolz tokens.
Euler Finance
Amount of Loss: ~ $197M
Analysis
The DeFi lending protocol Euler Finance was targeted, and the attackers profited by approximately 197 million US dollars.
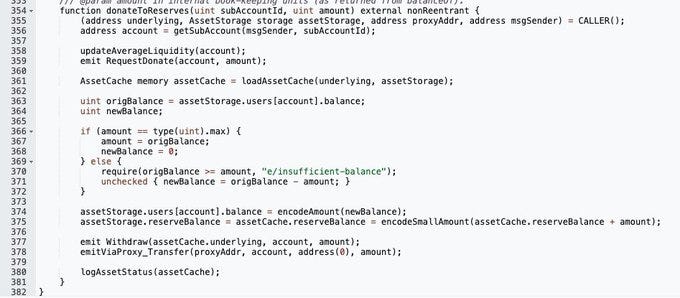
The attacker deposited funds using flash loans and then leveraged them twice to trigger the liquidation logic, donating the funds to the reserved address and performing a self-liquidation to collect any remaining assets.
Two critical factors contributed to the attack's success:
1. Money was given to the designated address without being subjected to a liquidity check.
This resulted in creating a mechanism that could directly cause soft liquidation.
2. When high leverage triggered the soft liquidation logic, the yield value increased, allowing the liquidator to obtain most of the collateral funds from the liquidated user's account by transferring only a portion of the liabilities to themselves.
The liquidator successfully passed their health factor check (
checkLiquidity) and withdrew the obtained funds because the collateral funds' value exceeded the liabilities' value (which were only partially transferred due to the soft liquidation).Yearn Finance
Amount of Loss: ~ $1.38M
Analysis
While there is no direct exposure to Euler, some vaults are indirectly exposed to the hack," Yearn Finance tweeted after the Euler hack.
Vaults using the Idle and Angle strategies have total exposure to yvUSDT and yvUSDC of $1.38 million.
The developers are working on the affected protocol, the Yearn Treasury will bear any remaining bad debt, and all vaults will remain open and fully operational for users as usual.
Idle Finance
Amount of Loss: ~ $10.99M
Analysis
After an investigation, the DeFi protocol Idle Finance tweeted that the estimated exposure of the Euler Finance vulnerability to the protocol Yield Tranches was $5.6628 million.
The estimated direction of Best Yield vaults was about $5.3271 million, for a total of about $10.99 million.
Yield Protocol
Amount of Loss: ~ $1.5M
Analysis
Euler phishing had an impact on the Yield Protocol mainnet liquidity pool. The Euler eTokens and Yield fyTokens are held in the Yield liquidity pool.
In a Twitter update, " all collateral deposited by borrowers on Yield Protocol appears to be safe," said Yield Protocol, a fixed-rate lending agreement.
Collateral is not deposited in Euler but is instead held in Yield Protocol. We still need exact figures for the total value of eTokens before the attack, but we believe it is less than $1.5 million.
Hedera
Amount of Loss: ~ $555K
Analysis
The attacker compromised the Hedera main network's smart contract service code and transferred Hedera Token Service tokens held by some user accounts to their accounts.
Accounts used as liquidity pools on multiple DEXs migrated to use the Hedera Token Service using Uniswap V2-derived contract generations, including Pangolin Hedera, SaucerSwap, and HeliSwap, were targeted by the attackers.
When attackers transferred tokens obtained from the attack to a Hashport Network bridge, bridge operators detected the activity and quickly disabled it.
To prevent attackers from stealing more tokens, Hedera disabled the mainnet proxy, preventing users from accessing the mainnet.
Explore the Depths of Knowledge: Research Papers & Blogs🔖
Best Cybersecurity Practices for Your Business
We have faced many challenges since the inception of Web3, but one of the most important and ongoing challenges that the web3 ecosystem faces today is security. The ever-increasing threats to web3 protocols indicate that web3 security is more important than ever. To protect their assets and data, businesses must implement strong cybersecurity practices.
Vulnerability in implementations of SHA-3
This paper describes a flaw in several implementations of the Secure Hash Algorithm 3 (SHA-3) made public by its designers. The vulnerability has existed since Keccak's final-round update was submitted to the National Institute of Standards and Technology (NIST) SHA-3 hash function competition in January 2011. It is in the Keccak team's eXtended Keccak Code Package (XKCP).
Tune in to Engaging Twitter Spaces & Webinars! 🎙️
Web3 Community Spotlight🔦
Moloch’s Vault A New CTF Challenge is Live!